Our Blog
Latest Blog & Articles
-
⚡ Weekly Recap: AI-Powered Phishing, Android Spying Tool, Linux Exploit, GitHub RCE & More
This week, the shadows moved faster than the patches. While most teams were still triaging last month’s alerts, attackers had already turned control panels into kill switches, kernels into open doors, and open-source pipelines into silent delivery systems. The game has shifted from breach to occupation. They’re living inside SaaS sessions, pushing code with trusted…
-
2026: The Year of AI-Assisted Attacks
On December 4, 2025, a 17-year-old was arrested in Osaka under Japan’s Unauthorized Access Prohibition Act. The young man had run malicious code to extract the personal data of over 7 million users of Kaikatsu Club, Japan’s largest internet cafe chain. When asked, the young man shared his motivation for the hack: he wanted to…
-
Critical cPanel Vulnerability Weaponized to Target Government and MSP Networks
A previously unknown threat actor has been observed targeting government and military entities in Southeast Asia, alongside a smaller cluster of managed service providers (MSPs) and hosting providers in the Philippines, Laos, Canada, South Africa, and the U.S., by exploiting the recently disclosed vulnerability in cPanel. The activity, detected by Ctrl-Alt-Intel on May 2, 2026,…
-
Global Crackdown Arrests 276, Shuts 9 Crypto Scam Centers, Seizes $701M
A coordinated international operation involving U.S. and Chinese authorities has arrested at least 276 suspects and shut down nine scam centers used for cryptocurrency investment fraud schemes targeting Americans, resulting in millions of dollars in losses. The crackdown was led by the Dubai Police, under the United Arab Emirates (UAE) Ministry of Interior, in partnership…
-
CISA Adds Actively Exploited Linux Root Access Bug CVE-2026-31431 to KEV
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added a recently disclosed security flaw impacting various Linux distributions to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild. The vulnerability, tracked as CVE-2026-31431 (CVSS score: 7.8), is a case of local privilege escalation (LPE) flaw that could allow…
-
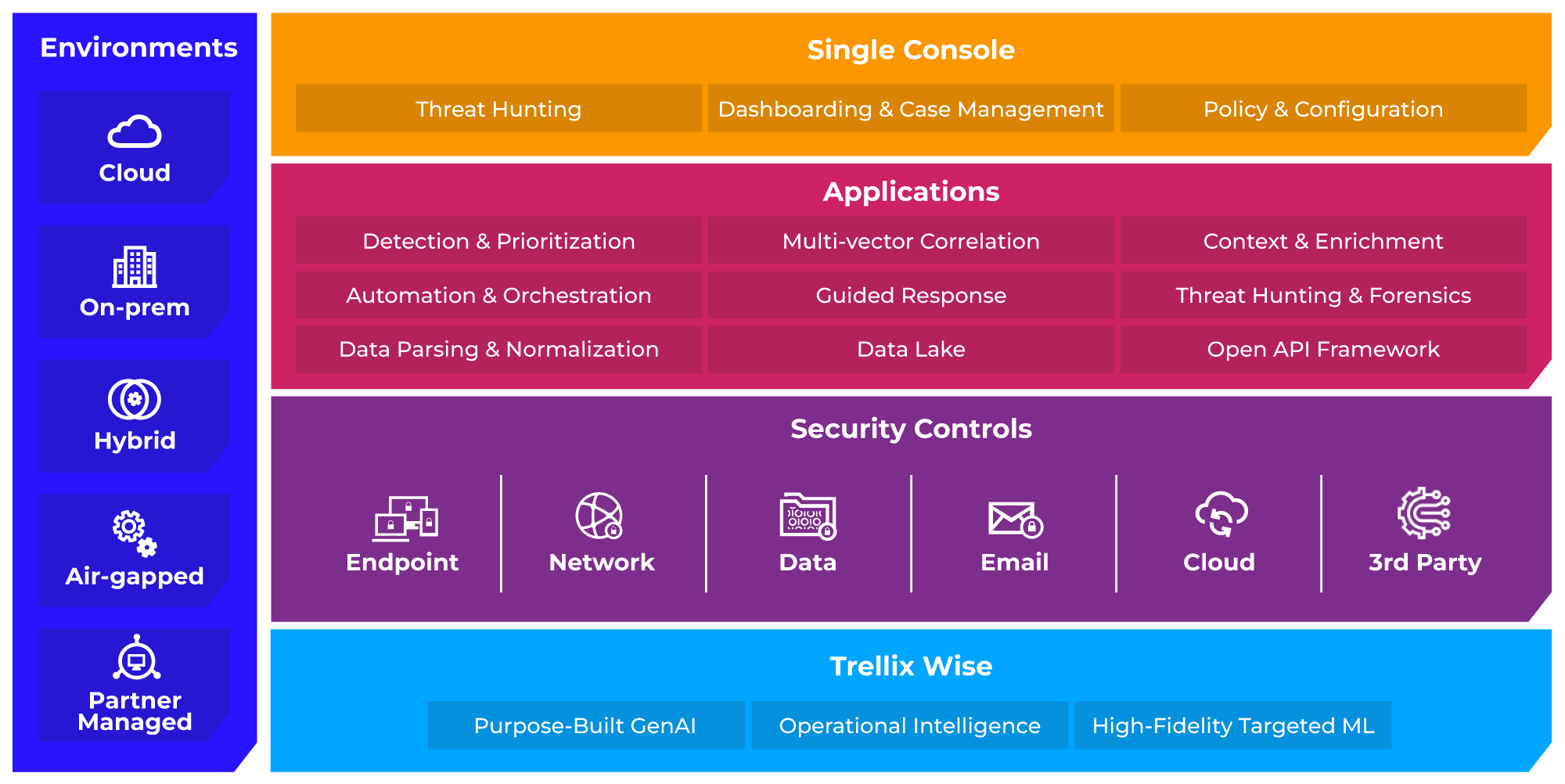
Trellix Confirms Source Code Breach With Unauthorized Repository Access
Cybersecurity company Trellix has announced that it suffered a breach that enabled unauthorized access to a “portion” of its source code. It said it “recently identified” the compromise of its source code repository and that it began working with “leading forensic experts” to resolve the matter immediately. It also said it has notified law enforcement…