-

Kremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
Polish government institutions have been targeted as part of a large-scale malware campaign orchestrated by a Russia-linked nation-state actor called APT28. “The campaign sent emails with content intended to arouse the recipient’s interest and persuade him to click on the link,” the computer emergency response team, CERT Polska, said in a Wednesday bulletin. Clicking on the link
-

New Guide: How to Scale Your vCISO Services Profitably
Cybersecurity and compliance guidance are in high demand among SMEs. However, many of them cannot afford to hire a full-time CISO. A vCISO can answer this need by offering on-demand access to top-tier cybersecurity expertise. This is also an opportunity for MSPs and MSSPs to grow their business and bottom line. MSPs and MSSPs that expand their offerings…
-

Mirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
Two recently disclosed security flaws in Ivanti Connect Secure (ICS) devices are being exploited to deploy the infamous Mirai botnet. That’s according to findings from Juniper Threat Labs, which said the vulnerabilities CVE-2023-46805 and CVE-2024-21887 have been leveraged to deliver the botnet payload. While CVE-2023-46805 is an authentication bypass flaw,
-
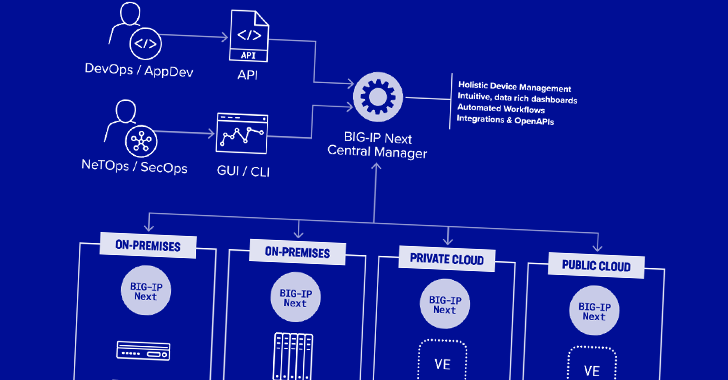
Critical F5 Central Manager Vulnerabilities Allow Enable Full Device Takeover
Two security vulnerabilities have been discovered in F5 Next Central Manager that could be exploited by a threat actor to seize control of the devices and create hidden rogue administrator accounts for persistence. The remotely exploitable flaws “can give attackers full administrative control of the device, and subsequently allow attackers to create accounts on any…
-

Major Oregon wine event in deal to grow global profile
International Pinot Noir Celebration, London-based Decanter join forces.
-

Oregon Hospital Association challenges ‘uniquely flawed’ M&A law
The Oregon Hospital Association sued over what it considers a vague law related to health care transactions.
-

Longtime Nike designer behind iconic Air Max shoes leaves company
Dylan Raasch was responsible for Air Max 270 and other top-selling sneakers from Nike.
-

Political Campaign Signs in the City’s Public Right-of-Way
THE DALLES — Over the past few weeks leading up to this month’s election, the City has been made aware of several political campaign signs located in the City’s public rights-of-way. Non-permitted signs located in the public right-of-way is a…
-

Providence Park renews KeyBank partnership with new community plaza
Providence Park’s northeast entrance is now KeyBank Community Plaza.
-

Technology Association of Oregon awards cybersecurity, food waste and AI startups
The annual awards from the Tech Association of Oregon celebrate the tech industry in Oregon and Southwest Washington.

