-
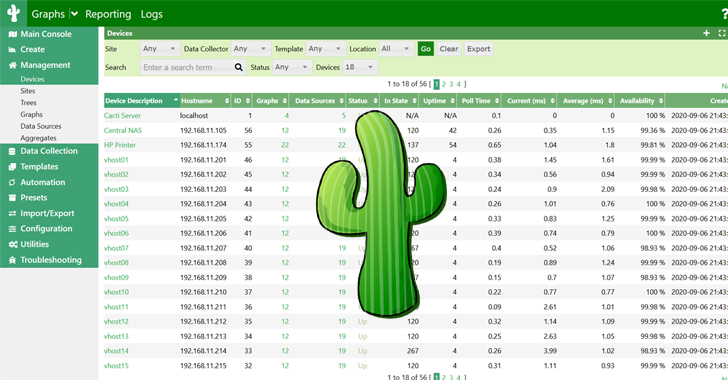
Critical Flaws in Cacti Framework Could Let Attackers Execute Malicious Code
The maintainers of the Cacti open-source network monitoring and fault management framework have addressed a dozen security flaws, including two critical issues that could lead to the execution of arbitrary code. The most severe of the vulnerabilities are listed below – CVE-2024-25641 (CVSS score: 9.1) – An arbitrary file write vulnerability in the “Package Import” feature that
-

6 Mistakes Organizations Make When Deploying Advanced Authentication
Deploying advanced authentication measures is key to helping organizations address their weakest cybersecurity link: their human users. Having some form of 2-factor authentication in place is a great start, but many organizations may not yet be in that spot or have the needed level of authentication sophistication to adequately safeguard organizational data. When deploying
-

Ongoing Campaign Bombards Enterprises with Spam Emails and Phone Calls
Cybersecurity researchers have uncovered an ongoing social engineering campaign that bombards enterprises with spam emails with the goal of obtaining initial access to their environments for follow-on exploitation. “The incident involves a threat actor overwhelming a user’s email with junk and calling the user, offering assistance,” Rapid7 researchers Tyler McGraw, Thomas Elkins, and
-

For Washington Trust, Vancouver, and its growing business base, beckons
The bank will feature commercial, small business, mortgage, private and retail banking and wealth management services.
-

As supply shifts, here’s how home prices are trending in the Portland area
One of the biggest reasons for high home prices is shifting, but that’s not the only factor shaping the market.
-

Willamette University leases space in the Pearl District
Willamette University is moving students into the Ecotrust building in the Pearl District.
-

Oregon hospitals scramble to hire nurses to comply with new law in June
Hospital systems must have their new safe staffing plans in place in June to comply with a law that passed last year.
-

Intel brings in industry veteran for key role in Gelsinger’s turnaround plan
Kevin O’Buckley started on Monday as senior vice president and general manager of foundry services, succeeding Stuart Pann, the company said.
-
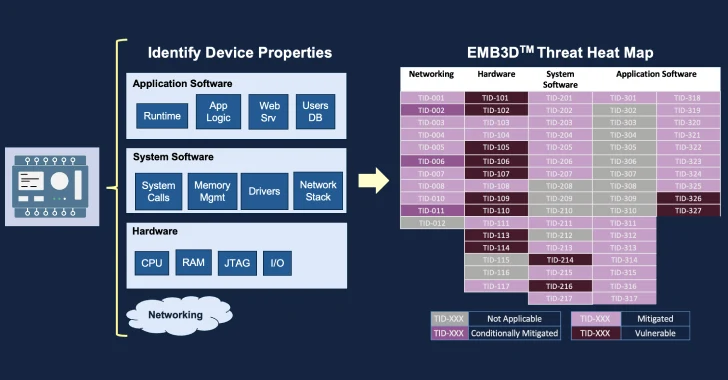
MITRE Unveils EMB3D: A Threat-Modeling Framework for Embedded Devices
The MITRE Corporation has officially made available a new threat-modeling framework called EMB3D for makers of embedded devices used in critical infrastructure environments. “The model provides a cultivated knowledge base of cyber threats to embedded devices, providing a common understanding of these threats with the security mechanisms required to mitigate them,” the non-profit said
-
The 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
With the browser becoming the most prevalent workspace in the enterprise, it is also turning into a popular attack vector for cyber attackers. From account takeovers to malicious extensions to phishing attacks, the browser is a means for stealing sensitive data and accessing organizational systems. Security leaders who are planning their security architecture

