-
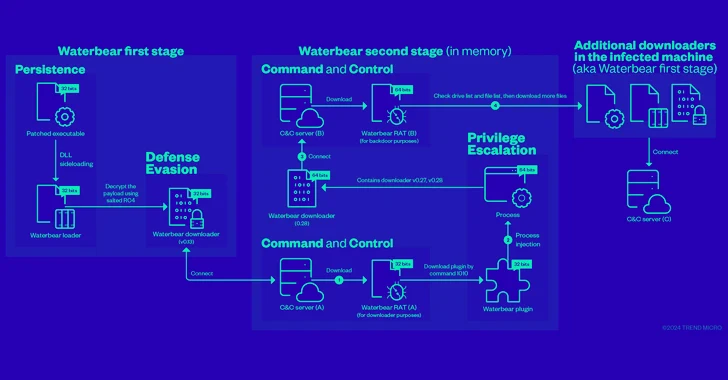
China-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
Cybersecurity researchers have shed more light on a remote access trojan (RAT) known as Deuterbear used by the China-linked BlackTech hacking group as part of a cyber espionage campaign targeting the Asia-Pacific region this year. “Deuterbear, while similar to Waterbear in many ways, shows advancements in capabilities such as including support for shellcode plugins, avoiding handshakes
-

Kimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
The Kimsuky (aka Springtail) advanced persistent threat (APT) group, which is linked to North Korea’s Reconnaissance General Bureau (RGB), has been observed deploying a Linux version of its GoBear backdoor as part of a campaign targeting South Korean organizations. The backdoor, codenamed Gomir, is “structurally almost identical to GoBear, with extensive sharing of code between
-

CISA Warns of Actively Exploited D-Link Router Vulnerabilities – Patch Now
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added two security flaws impacting D-Link routers to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The list of vulnerabilities is as follows – CVE-2014-100005 – A cross-site request forgery (CSRF) vulnerability impacting D-Link DIR-600 routers that allows an
-

Google Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
Google has rolled out fixes to address a set of nine security issues in its Chrome browser, including a new zero-day that has been exploited in the wild. Assigned the CVE identifier CVE-2024-4947, the vulnerability relates to a type confusion bug in the V8 JavaScript and WebAssembly engine. It was reported by Kaspersky researchers Vasily Berdnikov and Boris
-

NW Natural, facing ‘electrify everything’ headwind, embraces Bill Gates-backed tech
In a first, small amounts of clean-burning hydrogen are flowing into the NW Natural distribution system.
-
Leatherman CEO Ben Rivera on being a tinkerer and using an item he designed on a landmark day
Rivera became CEO of the Portland-founded family-owned company in 2013 after over two decades with the company as a manufacturing engineer.
-

Kotek looks to give Port of Portland $40M to keep Terminal 6 open
The Port has faced funding shortfalls and cuts that have resulted in what is projected to be a $14 million shortfall from container service this year.
-

Exclusive: Downtown Portland hotel once again faces foreclosure
Its owners are in danger of losing the upscale hotel thanks to lingering debt and a tepid market for guest rooms.
-

Sports Bra owner named Rose Festival parade grand marshal
Nguyen will be feted at an event she fondly remembers attending as a child.
-

New Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
Researchers have discovered a new security vulnerability stemming from a design flaw in the IEEE 802.11 Wi-Fi standard that tricks victims into connecting to a less secure wireless network and eavesdrop on their network traffic. The SSID Confusion attack, tracked as CVE-2023-52424, impacts all operating systems and Wi-Fi clients, including home and mesh networks that are based on

