-

Oregon is home to the world’s largest Dark Sky Sanctuary. Here’s how it happened.
“In my experience, nobody wants to light pollute.” Travel Southern Oregon’s Bob Hackett on landing the Oregon Outback International Dark Sky Sanctuary certification.
-

Moroccan Cybercrime Group Steals Up to $100K Daily Through Gift Card Fraud
Microsoft is calling attention to a Morocco-based cybercrime group dubbed Storm-0539 that’s behind gift card fraud and theft through highly sophisticated email and SMS phishing attacks. “Their primary motivation is to steal gift cards and profit by selling them online at a discounted rate,” the company said in its latest Cyber Signals report. “We’ve seen some examples where
-

Report: The Dark Side of Phishing Protection
The transition to the cloud, poor password hygiene and the evolution in webpage technologies have all enabled the rise in phishing attacks. But despite sincere efforts by security stakeholders to mitigate them – through email protection, firewall rules and employee education – phishing attacks are still a very risky attack vector. A new report by LayerX explores the state…
-

New Tricks in the Phishing Playbook: Cloudflare Workers, HTML Smuggling, GenAI
Cybersecurity researchers are alerting of phishing campaigns that abuse Cloudflare Workers to serve phishing sites that are used to harvest users’ credentials associated with Microsoft, Gmail, Yahoo!, and cPanel Webmail. The attack method, called transparent phishing or adversary-in-the-middle (AitM) phishing, “uses Cloudflare Workers to act as a reverse proxy server for a
-

Applying for SBA loans? 3 insights to clarify the process
For many small-business owners that are on an access-to-capital journey, the thought of pursuing an SBA (Small Business Administration) loan has no doubt crossed their minds. Some may seek out SBA loans, but for many the SBA process can seem daunting and overwhelming. The SBA was formed in 1953, and at the time the paperwork…
-

Pakistan-linked Hackers Deploy Python, Golang, and Rust Malware on Indian Targets
The Pakistan-nexus Transparent Tribe actor has been linked to a new set of attacks targeting Indian government, defense, and aerospace sectors using cross-platform malware written in Python, Golang, and Rust. “This cluster of activity spanned from late 2023 to April 2024 and is anticipated to persist,” the BlackBerry Research and Intelligence Team said in a technical report
-

Oregon wine industry is uncorking new tasting rooms despite a visitor slump
New tasting rooms abound with an emphasis on tailored “experiences.”
-

Tourism playbook: Signature sporting events are proving a formidable draw
“Our Super Bowl on the horizon is the 2030 Women’s Final Four.” Sport Oregon’s Matt Reed
-
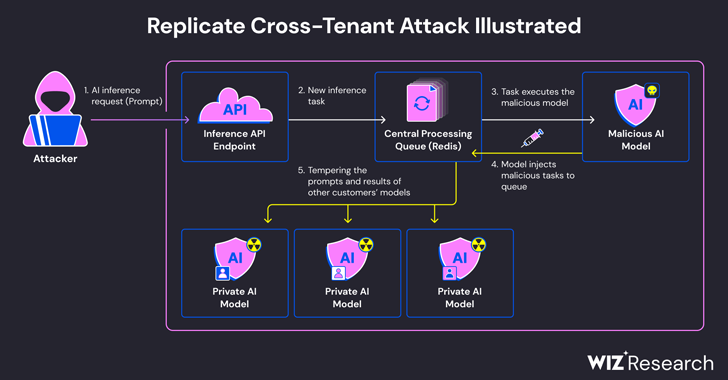
Experts Find Flaw in Replicate AI Service Exposing Customers’ Models and Data
Cybersecurity researchers have discovered a critical security flaw in an artificial intelligence (AI)-as-a-service provider Replicate that could have allowed threat actors to gain access to proprietary AI models and sensitive information. “Exploitation of this vulnerability would have allowed unauthorized access to the AI prompts and results of all Replicate’s platform customers,”
-

Editor’s notebook: Dropping in on Prosper Portland’s minority supplier roundtable
Representatives from more than 30 companies, including Intel, Salt & Straw, ZGF, Truebeck Construction, Swinerton, Leatherman Tool Group, OHSU, PGE and New Seasons Market gathered for a recent roundtable discussion on supplier diversity.

