-

Combatting the Evolving SaaS Kill Chain: How to Stay Ahead of Threat Actors
The modern kill chain is eluding enterprises because they aren’t protecting the infrastructure of modern business: SaaS. SaaS continues to dominate software adoption, and it accounts for the greatest share of public cloud spending. But enterprises and SMBs alike haven’t revised their security programs or adopted security tooling built for SaaS. Security teams keep jamming…
-

New SnailLoad Attack Exploits Network Latency to Spy on Users’ Web Activities
A group of security researchers from the Graz University of Technology have demonstrated a new side-channel attack known as SnailLoad that could be used to remotely infer a user’s web activity. “SnailLoad exploits a bottleneck present on all Internet connections,” the researchers said in a study released this week. “This bottleneck influences the latency of…
-
Hundreds of acres in Bend marketed for nearly 2,500 new homes
Some 2,500 new homes could one day rise on just over 260 acres in Central Oregon’s largest city.
-

$31M court clash between Nike, Avangrid put on ice
Judge Leslie Bottomly made it clear she doesn’t want further delays.
-

Portland Mayor Wheeler introduces new city administrators as charter reform takes shape
The new structure follows a vote in 2022 to overhaul Portland’s form of government.
-

Nike lowers annual, quarterly outlook after lackluster Q4 earnings
Nike now expects first-quarter revenue to be down 10% and full-year revenue to be down middle-single digits.
-

Chipotle gives new Trail Blazer Donovan Clingan a bowl of his own
The former UConn center hits town with a signature dish.
-

Rust-Based P2PInfect Botnet Evolves with Miner and Ransomware Payloads
The peer-to-peer malware botnet known as P2PInfect has been found targeting misconfigured Redis servers with ransomware and cryptocurrency miners. The development marks the threat’s transition from what appeared to be a dormant botnet with unclear motives to a financially motivated operation. “With its latest updates to the crypto miner, ransomware payload, and rootkit elements, it…
-
The Secrets of Hidden AI Training on Your Data
While some SaaS threats are clear and visible, others are hidden in plain sight, both posing significant risks to your organization. Wing’s research indicates that an astounding 99.7% of organizations utilize applications embedded with AI functionalities. These AI-driven tools are indispensable, providing seamless experiences from collaboration and communication to work management and
-
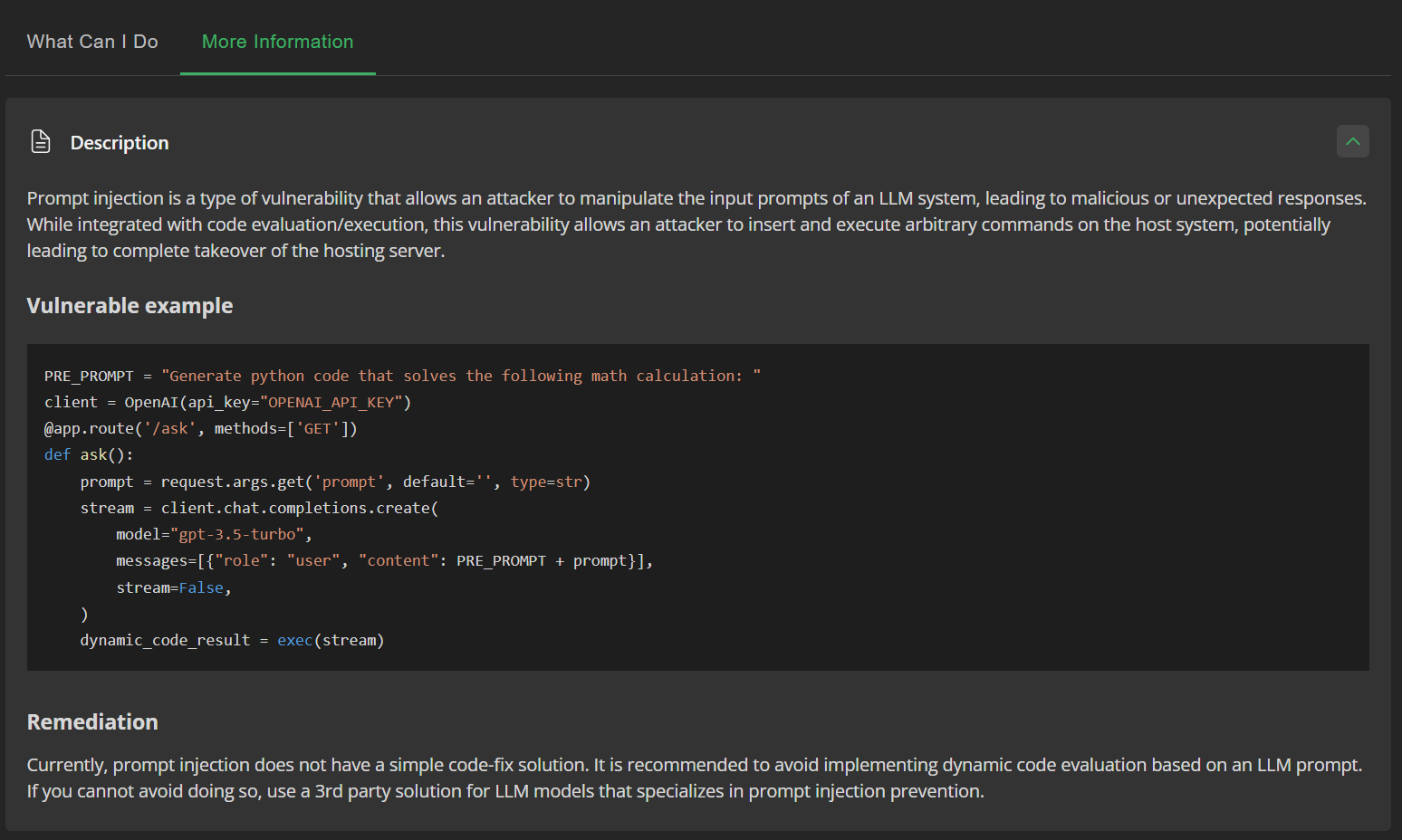
Prompt Injection Flaw in Vanna AI Exposes Databases to RCE Attacks
Cybersecurity researchers have disclosed a high-severity security flaw in the Vanna.AI library that could be exploited to achieve remote code execution vulnerability via prompt injection techniques. The vulnerability, tracked as CVE-2024-5565 (CVSS score: 8.1), relates to a case of prompt injection in the “ask” function that could be exploited to trick the library into executing…

