-

Hotel on Oregon State campus in legal battle over foreclosure
The Hilton Garden Inn on Oregon State University’s campus in Corvallis has been embroiled in a lengthy legal battle with its lender to avoid a foreclosure.
-

Uncertain 2025-26 budget could be exacerbated by federal executive orders
-

CRE Q&A: How Oregon can meet the growing need for senior housing
A worsening senior living housing shortage creates opportunities for commercial real estate developers and investors.
-

New OpenSSH Flaws Enable Man-in-the-Middle and DoS Attacks — Patch Now
Two security vulnerabilities have been discovered in the OpenSSH secure networking utility suite that, if successfully exploited, could result in an active machine-in-the-middle (MitM) and a denial-of-service (DoS) attack, respectively, under certain conditions. The vulnerabilities, detailed by the Qualys Threat Research Unit (TRU), are listed below – CVE-2025-26465 – The OpenSSH client
-

Photo: Hundreds rally on President’s Day
HOOD RIVER — On Feb. 17 — President’s Day — hundreds of Gorge residents made their way to downtown Hood River to protest the Trump administration and rally behind vulnerable populations. The Columbia Gorge Women’s Action Network organized the rally.
-

Bioscience industry in Oregon outpaces overall job growth
Oregon’s bioscience sector has been growing faster than the overall economy, but proposed federal budget cuts could slow its momentum.
-
Chinese Hackers Exploit MAVInject.exe to Evade Detection in Targeted Cyber Attacks
The Chinese state-sponsored threat actor known as Mustang Panda has been observed employing a novel technique to evade detection and maintain control over infected systems. This involves the use of a legitimate Microsoft Windows utility called Microsoft Application Virtualization Injector (MAVInject.exe) to inject the threat actor’s malicious payload into an external process, waitfor.exe,
-

New FrigidStealer Malware Targets macOS Users via Fake Browser Updates
Cybersecurity researchers are alerting to a new campaign that leverages web injects to deliver a new Apple macOS malware known as FrigidStealer. The activity has been attributed to a previously undocumented threat actor known as TA2727, with the information stealers for other platforms such as Windows (Lumma Stealer or DeerStealer) and Android (Marcher). TA2727 is…
-
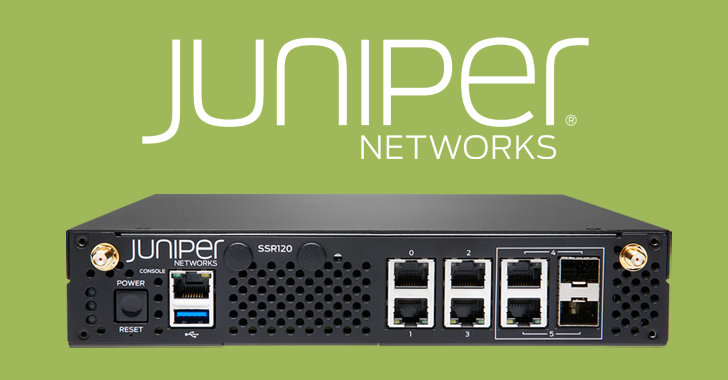
Juniper Session Smart Routers Vulnerability Could Let Attackers Bypass Authentication
Juniper Networks has released security updates to address a critical security flaw impacting Session Smart Router, Session Smart Conductor, and WAN Assurance Router products that could be exploited to hijack control of susceptible devices. Tracked as CVE-2025-21589, the vulnerability carries a CVSS v3.1 score of 9.8 and a CVS v4 score of 9.3. “An Authentication…
-

Debunking the AI Hype: Inside Real Hacker Tactics
Is AI really reshaping the cyber threat landscape, or is the constant drumbeat of hype drowning out actual, more tangible, real-world dangers? According to Picus Labs’ Red Report 2025 which analyzed over one million malware samples, there’s been no significant surge, so far, in AI-driven attacks. Yes, adversaries are definitely continuing to innovate, and while…

