-

Thousands without power in Portland region
More than 30,000 utility customers were without power Tuesday morning after heavy storms lashed the Portland region overnight.
-
5 Active Malware Campaigns in Q1 2025
The first quarter of 2025 has been a battlefield in the world of cybersecurity. Cybercriminals continued launching aggressive new campaigns and refining their attack methods. Below is an overview of five notable malware families, accompanied by analyses conducted in controlled environments. NetSupport RAT Exploiting the ClickFix Technique In early 2025, threat actors began exploiting a…
-

5 Common Cyber Threats in 2025 (and How To Avoid Them)
In 2025, cyber threats are in almost every nook and corner. They might be with the intent to destroy computers, steal data, or take money. Understanding what they are and how protection against them works will come in handy. What Are the Most Common Cyber Threats? They come in so many forms, some old, some…
-

FatalRAT Phishing Attacks Target APAC Industries Using Chinese Cloud Services
Various industrial organizations in the Asia-Pacific (APAC) region have been targeted as part of phishing attacks designed to deliver a known malware called FatalRAT. “The threat was orchestrated by attackers using legitimate Chinese cloud content delivery network (CDN) myqcloud and the Youdao Cloud Notes service as part of their attack infrastructure,” Kaspersky ICS CERT said…
-

Two Actively Exploited Security Flaws in Adobe and Oracle Products Flagged by CISA
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two security flaws impacting Adobe ColdFusion and Oracle Agile Product Lifecycle Management (PLM) to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerabilities in question are listed below – CVE-2017-3066 (CVSS score: 9.8) – A deserialization vulnerability impacting
-

It’s official: Largest Oregon nurses strike ends with ratification of contracts
The deals bring to a close a walkout that lasted more than six weeks.
-

Buffett’s Precision Castparts continues growth streak
Precision Castparts posted revenue growth for the third straight year in 2024, topping its pre-pandemic sales.
-

Oregon hospitals’ community benefit spending falls after decade-long rise
Hospitals in the state each have a minimum spending floor for community benefit activities and under-reimbursement.
-

Trump-Musk foreign aid freeze hits Portland area humanitarian organization
Medical Teams International has three main grants that receive funding from the federal government.
-
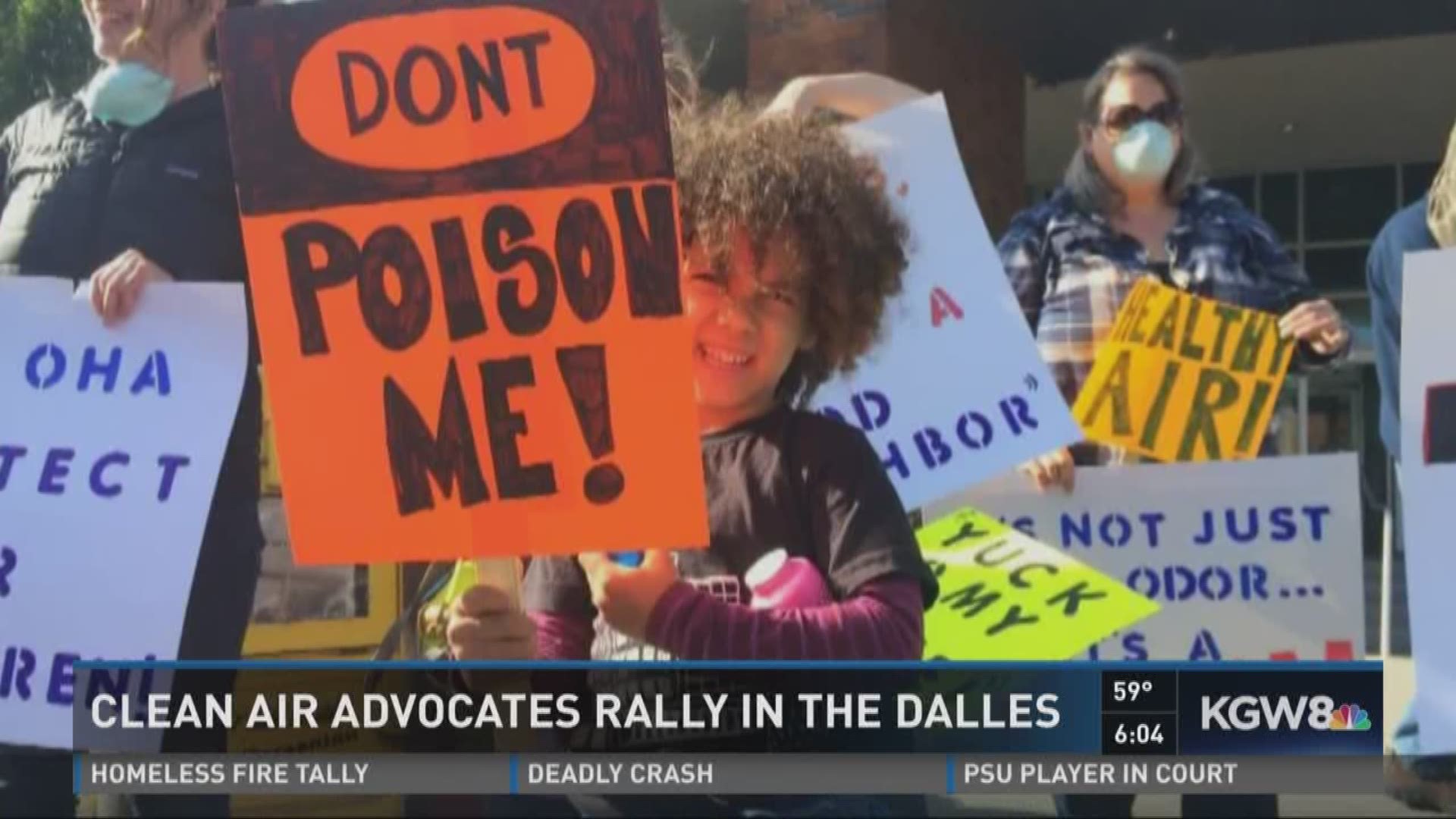
Friday protests begin in The Dalles (slideshow)
On Friday, Feb. 21, community members gathered at the cross street of Second and Union streets downtown The Dalles in protest of the Trump Administration. The protest was organized by local Indivisible and Wasco County Democrats members Connie Krummrich and…

