-

Port of Portland revokes DEI policy amid funding threat
Port Executive Director Curtis Robinhold said it faced the potential loss of $145 million in federal funding.
-
Kimsuky Exploits BlueKeep RDP Vulnerability to Breach Systems in South Korea and Japan
Cybersecurity researchers have flagged a new malicious campaign related to the North Korean state-sponsored threat actor known as Kimsuky that exploits a now-patched vulnerability impacting Microsoft Remote Desktop Services to gain initial access. The activity has been named Larva-24005 by the AhnLab Security Intelligence Center (ASEC). “In some systems, initial access was gained through
-

Intel invests billions in US chip manufacturing, aims to create 30,000 jobs across four states
Intel’s multibillion-dollar investment in U.S. chip manufacturing promises thousands of new jobs.
-
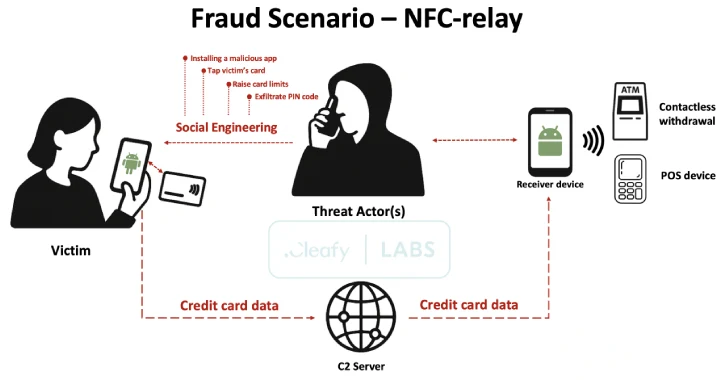
SuperCard X Android Malware Enables Contactless ATM and PoS Fraud via NFC Relay Attacks
A new Android malware-as-a-service (MaaS) platform named SuperCard X can facilitate near-field communication (NFC) relay attacks, enabling cybercriminals to conduct fraudulent cashouts. The active campaign is targeting customers of banking institutions and card issuers in Italy with an aim to compromise payment card data, fraud prevention firm Cleafy said in an analysis. There is evidence…
-
5 Reasons Device Management Isn’t Device Trust
The problem is simple: all breaches start with initial access, and initial access comes down to two primary attack vectors – credentials and devices. This is not news; every report you can find on the threat landscape depicts the same picture. The solution is more complex. For this article, we’ll focus on the device threat…
-

Hackers Abuse Russian Bulletproof Host Proton66 for Global Attacks and Malware Delivery
Cybersecurity researchers have disclosed a surge in “mass scanning, credential brute-forcing, and exploitation attempts” originating from IP addresses associated with a Russian bulletproof hosting service provider named Proton66. The activity, detected since January 8, 2025, targeted organizations worldwide, according to a two-part analysis published by Trustwave SpiderLabs last week. “Net
-
Top 10 Security Tips for Mobile App Users
Mobile applications have become an integral part of our lives. We use them to browse the internet, network, communicate, and much more. But they open us up to risks caused by fraudsters who may steal information or damage our phones. According to 2024 data from Asee, over 75% of published apps have at least one…
-

APT29 Deploys GRAPELOADER Malware Targeting European Diplomats Through Wine-Tasting Lures
The Russian state-sponsored threat actor known as APT29 has been linked to an advanced phishing campaign that’s targeting diplomatic entities across Europe with a new variant of WINELOADER and a previously unreported malware loader codenamed GRAPELOADER. “While the improved WINELOADER variant is still a modular backdoor used in later stages, GRAPELOADER is a newly observed…
-
Rogue npm Packages Mimic Telegram Bot API to Plant SSH Backdoors on Linux Systems
Cybersecurity researchers have uncovered three malicious packages in the npm registry that masquerade as a popular Telegram bot library but harbor SSH backdoors and data exfiltration capabilities. The packages in question are listed below – node-telegram-utils (132 downloads) node-telegram-bots-api (82 downloads) node-telegram-util (73 downloads) According to supply chain
-

ASUS Confirms Critical Flaw in AiCloud Routers; Users Urged to Update Firmware
ASUS has disclosed a critical security flaw impacting routers with AiCloud enabled that could permit remote attackers to perform unauthorized execution of functions on susceptible devices. The vulnerability, tracked as CVE-2025-2492, has a CVSS score of 9.2 out of a maximum of 10.0. “An improper authentication control vulnerability exists in certain ASUS router firmware series,”

