-

Oregon Ballet Theatre’s world premiere of ‘Marilyn’ breaks audience record
The production was the highest-grossing for any show OBT has staged in the Newmark Theatre.
-

Dayo teams Yeti, Patagonia to help you cut social media time
Portland startup Dayo is on a mission to help people use social media less through an app that rewards people with discounts for major brands like Nespresso, Yeti and Patagonia.
-
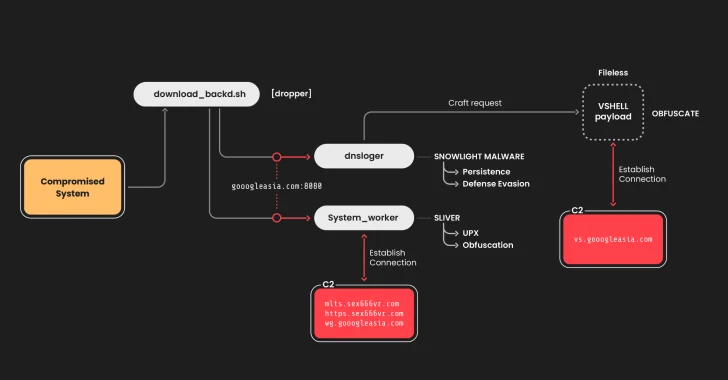
Chinese Hackers Target Linux Systems Using SNOWLIGHT Malware and VShell Tool
The China-linked threat actor known as UNC5174 has been attributed to a new campaign that leverages a variant of a known malware dubbed SNOWLIGHT and a new open-source tool called VShell to infect Linux systems. “Threat actors are increasingly using open source tools in their arsenals for cost-effectiveness and obfuscation to save money and, in…
-

Majority of Browser Extensions Can Access Sensitive Enterprise Data, New Report Finds
Everybody knows browser extensions are embedded into nearly every user’s daily workflow, from spell checkers to GenAI tools. What most IT and security people don’t know is that browser extensions’ excessive permissions are a growing risk to organizations. LayerX today announced the release of the Enterprise Browser Extension Security Report 2025, This report is the…
-

Is It Time for a Device Upgrade? Check for These 7 Signs
-
Crypto Developers Targeted by Python Malware Disguised as Coding Challenges
The North Korea-linked threat actor assessed to be behind the massive Bybit hack in February 2025 has been linked to a malicious campaign that targets developers to deliver new stealer malware under the guise of a coding assignment. The activity has been attributed by Palo Alto Networks Unit 42 to a hacking group it tracks…
-
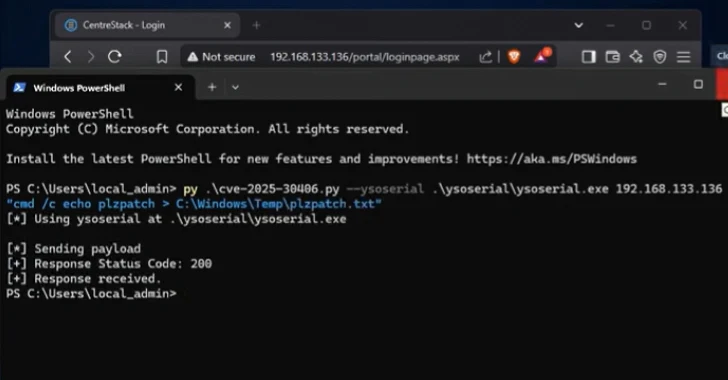
Gladinet’s Triofox and CentreStack Under Active Exploitation via Critical RCE Vulnerability
A recently disclosed security flaw in Gladinet CentreStack also impacts its Triofox remote access and collaboration solution, according to Huntress, with seven different organizations compromised to date. Tracked as CVE-2025-30406 (CVSS score: 9.0), the vulnerability refers to the use of a hard-coded cryptographic key that could expose internet-accessible servers to remote code execution attacks
-

AtkinsRealis completes $300M stake in Portland’s David Evans and Associates
A Canadian engineering and nuclear company has completed a deal for 70% of Portland’s David Evans and Associates.
-

Oregon winery staying in beverage giant’s fold
Lingua Franca among high-end wineries that Constellation Brands will retain.
-

Portland furniture company to move showroom to historic Pearl District building
The Joinery first opened its showroom on Southwest Yamhill Street in 2015.

